Top 10 Web3 hacks of 2023 constituted nearly 70% of total losses
For each type of Web3 attack, there is a distinct approach to safety. The comprehensive report prepared by the expert team at Salus explains how to go about each of them.
In 2023, the Web3 security landscape witnessed both resilience and challenges, with cyberattacks causing losses exceeding $1.7 billion across 453 reported incidents, according to Salus, a research-driven web3 security company.
Notable trends included a decline in overall losses, contrasting with high-profile exploits like Mixin Network’s $200 million loss, Euler Finance’s $197 million loss, and Multichain’s $126.36 million loss.
Common vulnerability in access control issues
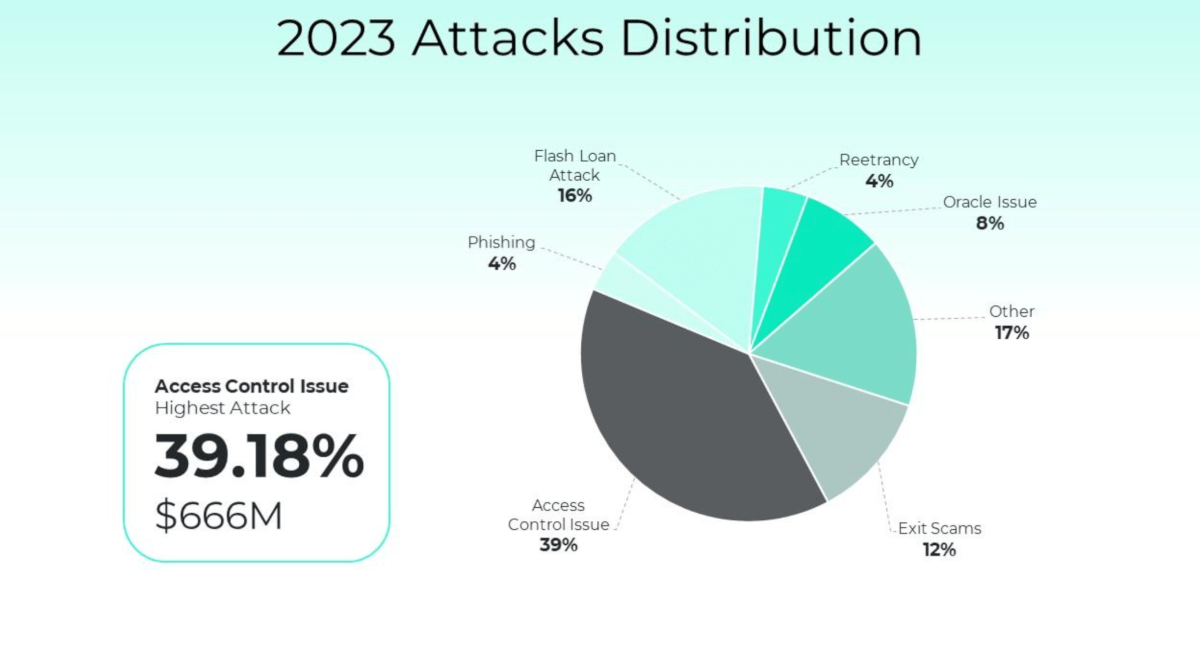
Vulnerabilities were diverse, with exit scams, access control issues, phishing, flash loan attacks, reentrancy, Oracle issues, and other vulnerabilities contributing to losses. Safety measures highlighted thorough project research, caution regarding high-return promises, robust access control mechanisms, Web3 penetration testing, and protective measures against flash loan attacks and reentrancy vulnerabilities.
The top 10 hacks of 2023, constituting nearly 70% of total losses, revealed a common vulnerability in access control issues, particularly private key thefts. Lazarus Group played a significant role in multiple breaches, draining funds from compromised hot wallets.
Major incidents included Mixin Network’s cloud breach, Euler Finance’s vulnerability exploit, Multichain’s asset movement, Poloniex’s Lazarus Group hack, BonqDAO’s oracle manipulation, Atomic Wallet’s North Korean Lazarus Group attack, HECO Bridge and HTX losses, Curve and Vyper’s compiler bug, AlphaPo’s sophisticated phishing, and CoinEx’s compromised private key.
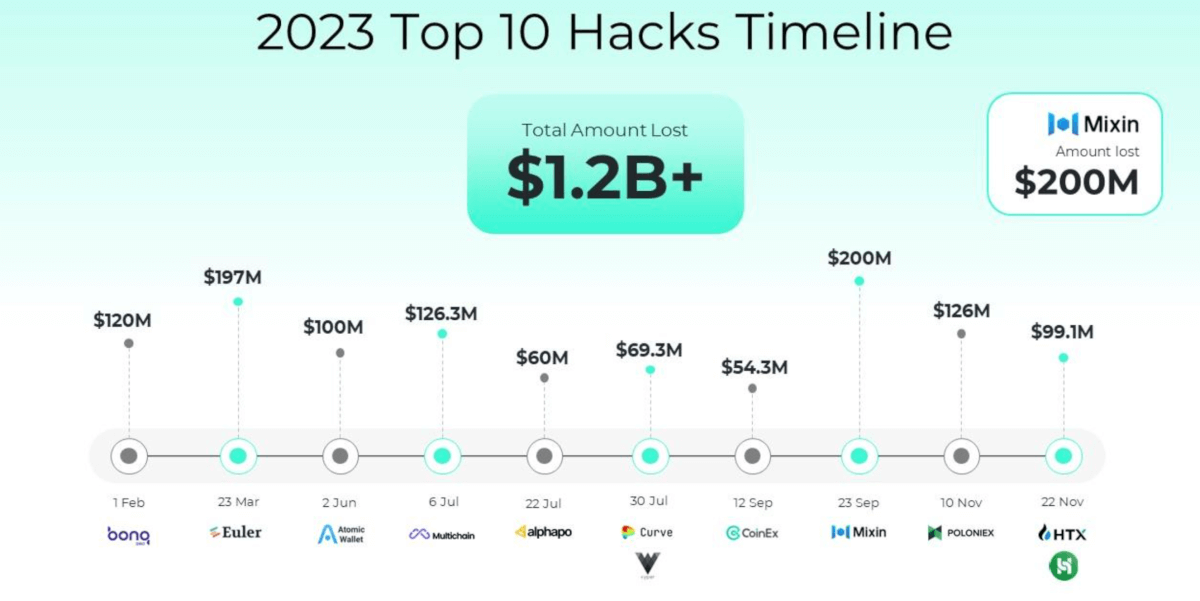
Despite reduced total losses compared to the previous year, the concentration of losses in the top 10 hacks highlights the need for improved security measures. Rigorous auditing, Web3 penetration testing, and heightened awareness are crucial, especially in light of evolving infiltration methods demonstrated by the Lazarus Group attacks.
How to be safe in Web3
For each type of Web3 attack, there is a distinct approach to safety. The comprehensive report prepared by the expert team at Salus explains how to go about each of them.
Exit Scams:
- Conduct thorough research on projects and teams, prioritizing those with a solid track record and transparent security assessments.
- Exercise caution with projects promising unrealistically high returns, and diversify investments to mitigate risks.
Access Control Issues:
- Implement robust authentication and authorization mechanisms, following the principle of least privilege.
- Regularly update access permissions and provide ongoing security training for employees, especially those with high privileges.
- Establish comprehensive monitoring systems to detect and respond promptly to any suspicious activities across infrastructure and applications.
Phishing:
- Conduct Web3 penetration testing to identify vulnerabilities in front-end security.
- Prioritize user education, encourage the use of hardware wallets and multi-factor authentication (MFA).
- Employ email verification and domain monitoring to enhance phishing prevention measures.
Flash Loan Attacks:
- Mitigate flash loan risks by implementing restrictions such as minimum borrowing amounts and time limits.
- Introduce fees for flash loan usage to deter attackers and raise the cost of malicious exploits.
Reentrancy:
- Adhere strictly to the Check-Effect-Interaction Model, running necessary checks and validations before state changes.
- Implement comprehensive reentry protection for functions involving sensitive operations within the contract.
- Conduct thorough smart contract audits by experienced and responsible auditors to mitigate reentrancy vulnerabilities.
Oracle Issues:
- Avoid using markets with shallow liquidity for price predictions.
- Assess token liquidity before integrating specific price oracle plans into your platform.
- Increase the attacker’s manipulation cost through Time-Weighted Average Price (TWAP) to enhance oracle vulnerability protection.